SONIC - Security Oriented Nexus for Intelligent Commodity solutions marketplace
 SONIC aims
to strengthen cyber resilience across diverse
infrastructures by delivering AI-powered, privacy-preserving
cybersecurity technologies through an intelligent marketplace that
supports regulatory compliance, collaboration, and explainable
decision-making across the EU cybersecurity ecosystem. SONIC, under
project number 101249631, is funded through the
DIGITAL-ECCC-2024-DEPLOY-CYBER-07 call and addresses the topic
DIGITAL-ECCC-2024-DEPLOY-CYBER-07-KEYTECH. The project is
implemented as a DIGITAL JU SME Support Action and is granted by the
European Cybersecurity Industrial, Technology and
Research Competence Centre.
SONIC aims
to strengthen cyber resilience across diverse
infrastructures by delivering AI-powered, privacy-preserving
cybersecurity technologies through an intelligent marketplace that
supports regulatory compliance, collaboration, and explainable
decision-making across the EU cybersecurity ecosystem. SONIC, under
project number 101249631, is funded through the
DIGITAL-ECCC-2024-DEPLOY-CYBER-07 call and addresses the topic
DIGITAL-ECCC-2024-DEPLOY-CYBER-07-KEYTECH. The project is
implemented as a DIGITAL JU SME Support Action and is granted by the
European Cybersecurity Industrial, Technology and
Research Competence Centre.
Effective Software Monitoring Leveraging Hardware Debugging Extensions
 This project aims to develop technologies that leverage debugging
features found on modern processors to efficiently monitor and apply
security policies on software, using decoupled reference monitors (RM)
running in parallel. It is supported by the Defense Advanced Research
Projects Agency (DARPA) through contract D21AP10116-00.
This project aims to develop technologies that leverage debugging
features found on modern processors to efficiently monitor and apply
security policies on software, using decoupled reference monitors (RM)
running in parallel. It is supported by the Defense Advanced Research
Projects Agency (DARPA) through contract D21AP10116-00.
ABIDES: Adaptive BInary DEbloating and Security
 This project aims to reduce the attack surface of binaries by:
hiding and removing unused library and kernel code,
disabling unwanted and potentially buggy features, and
specializing APIs.
It is supported by the
Office of Naval Research (ONR) through contract N00014-17-1-2788.
This project aims to reduce the attack surface of binaries by:
hiding and removing unused library and kernel code,
disabling unwanted and potentially buggy features, and
specializing APIs.
It is supported by the
Office of Naval Research (ONR) through contract N00014-17-1-2788.
Trails: Efficient Data-Flow Tracking Through HW-assisted Parallelization
 This project investigates a novel architecture for efficiently
performing dynamic data-flow tracking through hardware-assisted
parallelization. In particular, exploiting debugging extensions found
in modern CPUs. It is supported by the Defense Advanced Research
Projects Agency (DARPA) through contract FA8650-16-C-7662.
This project investigates a novel architecture for efficiently
performing dynamic data-flow tracking through hardware-assisted
parallelization. In particular, exploiting debugging extensions found
in modern CPUs. It is supported by the Defense Advanced Research
Projects Agency (DARPA) through contract FA8650-16-C-7662.
Adapting Static and Dynamic Program Analysis to Effectively Harden Debloated Software
 This project aims to harden debloated software by leveraging static
and dynamic analysis. The aim is to increase the effort required to
compromise software through techniques applied dynamically on
binaries, as well as the late stages of compilation, where some source-code
information may not be available. It is supported by the
Office of Naval Research (ONR) through grant N00014-16-1-2261.
This project aims to harden debloated software by leveraging static
and dynamic analysis. The aim is to increase the effort required to
compromise software through techniques applied dynamically on
binaries, as well as the late stages of compilation, where some source-code
information may not be available. It is supported by the
Office of Naval Research (ONR) through grant N00014-16-1-2261.
Authentication Using Glass Wearable Devices
 We are working on a new project that will assist users, specially
users with difficulties using their hands, to authenticate with
terminals without the use of their hands.
We are working on a new project that will assist users, specially
users with difficulties using their hands, to authenticate with
terminals without the use of their hands.
Cyber-physical Authentication
 Use the Internet of Things to model user movement and location for
authentication purposes.
Use the Internet of Things to model user movement and location for
authentication purposes.
MINESTRONE
 MINESTRONE is a novel architecture that integrates static analysis,
dynamic confinement, and code diversification techniques to enable the
identification, mitigation and containment of a large class of
software vulnerabilities. Our techniques will protect new software, as
well as already deployed (legacy) software by transparently inserting
extensive security instrumentation. They will also leverage concurrent
program analysis (potentially aided by runtime data gleaned from
profiling software) to gradually reduce the performance cost of the
instrumentation by allowing selective removal or refinement.
MINESTRONE is a novel architecture that integrates static analysis,
dynamic confinement, and code diversification techniques to enable the
identification, mitigation and containment of a large class of
software vulnerabilities. Our techniques will protect new software, as
well as already deployed (legacy) software by transparently inserting
extensive security instrumentation. They will also leverage concurrent
program analysis (potentially aided by runtime data gleaned from
profiling software) to gradually reduce the performance cost of the
instrumentation by allowing selective removal or refinement.
MINESTRONE will also use diversification techniques for confinement and fault-tolerance purposes. To minimize performance impact, our project will also leverage multi-core hardware or (when unavailable) remote servers to enable the quick identification of potential compromises.
The developed techniques will require no specific hardware or operating system features, although they will take advantage of such features where available, to improve both runtime performance and vulnerability coverage.
Funded by the AFRL.
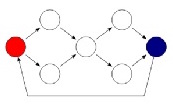
MEERKATS
 MEERKATS is a novel architecture for cloud environments that
elevates continuous system evolution, adaptation, and misdirection as
first-rate design principles. Our goal is to enable an environment for
cloud services that constantly changes along several dimensions,
toward creating an unpredictable target for an adversary. This
unpredictability will both impede the adversary’s ability to achieve
an initial system compromise and, if a compromise occurs, to detect,
disrupt, and/or otherwise impede his ability to exploit this success.
Thus, we envision an environment where cloud services and data are
constantly in flux, using adaptive (both proactive and reactive)
protection mechanisms and distributed monitoring at various levels of
abstraction. MEERKATS will effectively exploit “economies of scale”
(in resources available) to provide higher flexibility and
effectiveness in the deployment and use of protection mechanisms as
and where needed, focusing on current and anticipated mission needs
instead of an inefficient, “blanket” approach to protecting
“everything, all the time” at the same level of intensity.
MEERKATS is a novel architecture for cloud environments that
elevates continuous system evolution, adaptation, and misdirection as
first-rate design principles. Our goal is to enable an environment for
cloud services that constantly changes along several dimensions,
toward creating an unpredictable target for an adversary. This
unpredictability will both impede the adversary’s ability to achieve
an initial system compromise and, if a compromise occurs, to detect,
disrupt, and/or otherwise impede his ability to exploit this success.
Thus, we envision an environment where cloud services and data are
constantly in flux, using adaptive (both proactive and reactive)
protection mechanisms and distributed monitoring at various levels of
abstraction. MEERKATS will effectively exploit “economies of scale”
(in resources available) to provide higher flexibility and
effectiveness in the deployment and use of protection mechanisms as
and where needed, focusing on current and anticipated mission needs
instead of an inefficient, “blanket” approach to protecting
“everything, all the time” at the same level of intensity.
Funded by DARPA.
WOMBAT
 The WOMBAT
(Worldwide Observatory of Malicious Behaviors and Attack
Threats) project aims to develop malware collectors, analysis
techniques and a repository for Internet threat analysis.
The WOMBAT
(Worldwide Observatory of Malicious Behaviors and Attack
Threats) project aims to develop malware collectors, analysis
techniques and a repository for Internet threat analysis.
Funded by the EU FP7.
DeWorm
 The DeWorm project combines flow-based approaches to intrusion
detection with payload scanning to detect and stop flash worms.
The DeWorm project combines flow-based approaches to intrusion
detection with payload scanning to detect and stop flash worms.
Funded by STW Sentinels.